Legal review
Can anyone explain what the system sees, cites, stores, and returns without hand-waving?
01 / Launch briefing
Agentic Secure Group
ASG exists for the moment when legal, security, and delivery stop nodding along and start asking different questions about the same system. The first briefing gets the work framed once. After that, the right company owns the next move.
The team behind ASG includes a former Marine Corps judge advocate and a NeurIPS-published machine learning engineer who built the AI evaluation methodology that AISF now publishes.
15-minute call. No pitch. No retainer required.
Legal review
Can anyone explain what the system sees, cites, stores, and returns without hand-waving?
Security review
Can the team say where it runs, who controls it, and what evidence exists before it ships?
Real deployment
Can operators inherit it without rebuilding the environment or rewriting the workflow from scratch?
Procurement fit
Does the contract vehicle accommodate the cost model, performance period, and scope? Who signs first — prime, CO, or customer?
How the five-company model works
ASG is the routing layer in front of five specialist operators. That split is deliberate: legal trust, governance, model work, product delivery, and constrained deployment should not collapse into one vague AI shop story.
MRI
Defense / Intelligence
IC and defense work with cybersecurity, CMMC, or restricted-environment deployment requirements
IPSA
Legal / Compliance
private legal AI
AISF
Standards / Certification
standards and governance
ASI
Engineering / Infrastructure
IP development and AI product innovation
Agent Xero
Software Engineering / Full-Stack Development
application delivery
Published legal-AI research shows that hallucination risk remains material even in tools marketed as reliable. In high-consequence settings, questions about data boundaries, citation integrity, and auditability surface before a pilot becomes production.
The studies cited here are specific to legal tasks, not every AI workflow. But they illustrate the broader review problem: stakeholders will ask where the system runs, how outputs are grounded, and what evidence exists when the answer matters.
General-purpose legal query testing
58%-88%ChatGPT 4 to Llama 2 · Specific, verifiable questions about random federal court cases
Dahl et al., 16 J. Legal Analysis 64 (2024)Legal research tools using RAG
17%-33%Lexis+ AI and Thomson Reuters tools · Preregistered evaluation of legal research queries
Magesh et al., arXiv:2405.20362 (Stanford CodeX Lab, 2024)Published peer-reviewed ranges are shown here. This page does not publish an internal ASG benchmark or generalize these results beyond the tasks those studies actually tested.
Peer-reviewed research
ChatGPT 4 to Llama 2 hallucinated 58%-88% on specific, verifiable federal case queriesOur response
Private cloud, on-prem, and isolated deployment patterns are part of the menu when the environment requires tighter control.
High-stakes workflows can route low-confidence or source-conflicted outputs into human review instead of straight to action.
Frameworks such as NIST AI RMF, ISO/IEC 42001, and CMMC can shape logging, review, and evidence design early instead of appearing as retrofit work.
Supervised fine-tuning and other task-specific adaptation methods belong on the table when prompt scaffolding alone will not survive review.
Most vendors make the convenient architectural choice. In regulated environments, that is usually the choice that gets blocked later. This is where our build decisions break from the default.
Six places we part ways with the default build
Model architecture
Others: Generic hosted model plus prompt scaffolding
ASG: Task-specific model adaptation and evaluation when the workflow demands it
Data residency
Others: Sensitive processing outside the boundary your reviewers prefer
ASG: Private cloud, on-prem, or isolated deployment paths when the environment requires them
Deployment model
Others: Vendor-defined SaaS path with provider-managed updates
ASG: Cloud, on-prem, or isolated deployment options shaped to the review context
Hallucination handling
Others: Post-hoc disclaimers after the answer is already out
ASG: Grounding, citations, abstention, and human review where the workflow requires it
Security posture
Others: Shared-tenancy defaults plus perimeter controls
ASG: Private deployment patterns, segmentation, and review-driven security controls
Engagement model
Others: Separate sales motion from the people who ship
ASG: Technical scoping with the team responsible for implementation
02 / Decision scenes
Each route strips away the rest of the corporate story and shows the exact kind of conversation that should happen next.
Six entry lanes
IC and defense program leaders
Open full pathProgram leads, mission owners, and security officers trying to scope AI, cybersecurity, or CMMC work for IC and defense environments.
Likely lead
MRI leads when the work sits inside IC or defense programs and carries cybersecurity, CMMC, or controlled deployment requirements.
Visit lead siteWhat gets blocked first
The conversation usually stalls when security, infrastructure, and mission owners realize the pilot never answered where the model runs, who operates it, and what happens when connectivity disappears.
What has to be true
The system has to match the environment: private when needed, controlled when required, air-gapped when the program demands it, and accountable enough to survive scrutiny after deployment.
Why ASG first
ASG keeps the first call from splitting into parallel threads. The work gets framed once, then MRI owns the part that belongs inside IC and defense delivery.
What gets sorted first
ASG gets mission owners, security stakeholders, and technical constraints aligned before scoping starts.
Primary concerns
Proof in context
Operating signal
MRI's public site lists Reston, VA, CAGE 10S34, and CMMC Registered Practitioner status and frames its work around cybersecurity, controlled delivery, and restricted environments.
Build path
When the program needs model adaptation or private infrastructure, ASI joins the backbone instead of forcing a one-shop story that does not match the work.
Application layer
Operator tools or mission-facing interfaces shift the handoff toward Agent Xero without changing MRI's lead on the constrained environment itself.
Typical next move
Start with ASG. MRI leads the first scope for IC and defense work that includes cybersecurity, CMMC, or restricted-environment deployment requirements, then pulls in ASI or Agent Xero only where the build requires it.
ASI joins when model adaptation, evaluation, or private infrastructure are part of the job. Agent Xero joins if operator tooling or application delivery is in scope.
Best to bring
03 / Ownership ledger
ASG is the coordination layer at the front of the conversation. The operating companies remain distinct so ownership stays clear instead of collapsing into one vague generalist offer.
Mojave Research Inc.
IC and defense work with cybersecurity, CMMC, or restricted-environment deployment requirements
When it leads
The work lands in IC or defense and carries cybersecurity, CMMC, or controlled deployment requirements.
Where others join
ASI joins for model and infrastructure work. Agent Xero joins if operator tooling or application delivery enters scope.
Visible proof
MRI's public site lists Reston, VA, CAGE 10S34, and CMMC Registered Practitioner status. It also says cleared personnel for delivery are confirmed during contracting and highlights secure-enclave and air-gapped delivery environments.
IPSA Intelligent Systems Inc.
private legal AI
When it leads
The immediate question is legal usefulness under private control, with privilege and review trust still intact.
Where others join
ASI joins only when the legal workflow needs deeper private infrastructure, hardening, or model integration work.
Visible proof
IPSA's public site positions private-cloud or on-prem legal AI for research and matter workflows, with coaching and evaluation up front and source-grounded outputs at the core of the product story.
AI Security Foundation
standards and governance
When it leads
The first blocker is governance posture, control language, or the assurance story around the system.
Where others join
MRI and ASI join when the conversation moves from standards into implementation, validation, or operational hardening.
Visible proof
AISF was formally incorporated as a 501(c)(6) in November 2025. It houses the AI security standards work already underway through MRI's IC and defense engagements, and is building an AI Security Controls Matrix mapped to NIST AI RMF, MITRE ATLAS, ISO/IEC 42001, and OWASP guidance. Manbir Gulati, founding director and president, authored the AI evaluation methodology AISF now publishes as open standards.
Agentic Secure Inc.
IP development and AI product innovation
When it leads
The hard part lives in model behavior, private infrastructure, training pipelines, or deployment architecture.
Where others join
Agent Xero joins when the system also needs a product surface, operator workflow, or application delivery track.
Visible proof
ASI is the IP development and innovation engine within the ASG operating model — taking ideas into top-end AI products, owning the intellectual property, and building the systems that move from concept into production-grade delivery.
Agent Xero
application delivery
When it leads
The pressure is on the application layer: operator UX, product logic, shipping cadence, or full-stack delivery.
Where others join
ASI joins when the application depends on deeper model and infrastructure work underneath the product surface.
Visible proof
Agent Xero's public site centers private software delivery, code review, and custom builds for teams that need product and application execution rather than infrastructure work alone.
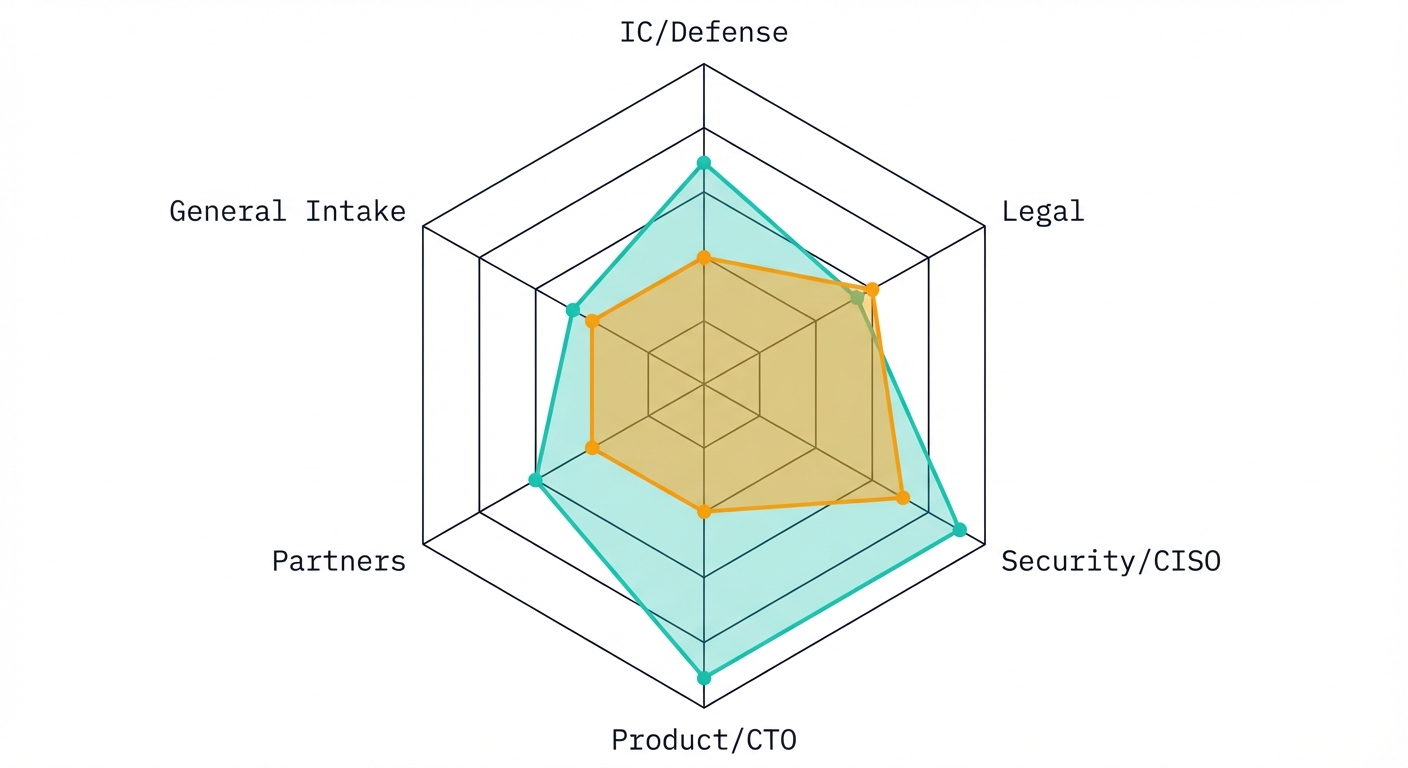
Fig. 2 — Operating entity coverage by domain. Filled = primary lead. Dot = supporting role.
The split is deliberate. One front-door briefing is useful only if the ownership after that briefing is unmistakable.
Review supporting materials
04 / Briefing questions
The point of the first briefing is to clarify ownership and next steps quickly, not to perform a long generic discovery ritual.
Initial contact
One email or form submission — no intake form, no pre-qualification.
ASG reads the context
Ownership, data constraints, and delivery model are assessed before a reply.
Entity handoff
The right operating company takes the next call — MRI, IPSA, AISF, ASI, or Agent Xero.
Delivery begins
Lead responsibility stays visible. No repeat briefings required.
Because the same system can simultaneously be a legal liability, a security boundary, and a procurement challenge — and no single generalist handles all three without diluting one of them. The five-entity model exists so the attorney reviewing privilege risk and the engineer building the deployment control don't report to the same commercial incentive. When ownership is explicit, accountability is explicit. That is what makes the handoff defensible. Each entity carries distinct authority, liability, and expertise. A defense contractor under CMMC obligations cannot share compliance scope with a legal AI firm whose privilege controls must stay inside the firm. A standards body whose credibility depends on independence cannot also be the operator selling systems against those standards. The five-entity structure is the answer to a structural conflict problem, not a holding company with divisions. Each entity — MRI, IPSA, AISF, ASI, and Agent Xero — is separately responsible for its own work, its own compliance, and its own delivery.
Because the hard part is rarely the demo. It is getting the right reviewers into the same conversation before the work stalls. ASG organizes that first read and routes the next call cleanly.
No. Use the path that feels closest, or use the general path if the lane is mixed. ASG sorts out who should lead, who should support, and who needs to be on the next call.
No. MRI, IPSA, AISF, ASI, and Agent Xero remain responsible for their own work. ASG handles the first read and the handoff.
Mojave Research Inc. leads IC and defense work with cybersecurity, CMMC, and restricted-environment deployment requirements. Its public site lists CMMC Registered Practitioner status and notes that cleared delivery is confirmed during contracting.
IPSA Intelligent Systems Inc. leads private legal AI matters where privilege, firm control, and matter-specific workflow design are non-negotiable.
AI Security Foundation handles standards, control language, and assurance framing. When the work turns operational, MRI and ASI step in where needed.
Agentic Secure Inc. is the IP development and innovation engine — it takes ideas into top-end AI products, owns the intellectual property, and builds the systems that move from concept into production-grade delivery.
Yes. Mojave Research Inc. lists CMMC Registered Practitioner status on its public site. Specific assessment scopes, certification levels, and cleared delivery arrangements are confirmed at the contracting stage rather than in the briefing phase.
Mojave Research Inc. holds CAGE code 10S34 and is based in Reston, VA. Federal buyers and primes can use this to verify MRI's entity registration in SAM.gov before engaging.
MRI is the operating entity for federal and defense work. Engagement path, contract vehicle, and scope — including CUI handling, controlled environment requirements, and compliance obligations — are confirmed during the briefing and contracting phase. Use the defense path or the general path to start.
CUI handling requirements are addressed at the contracting level with MRI. When a program carries CUI, ITAR, or other controlled data obligations, MRI handles the scope and delivery model. Raise it in the briefing so the right operating entity can confirm the arrangement.
The initial briefing is a working conversation, not a sales call — there is no charge for the first session. Engagements are scoped and priced after the briefing, when the right entity has been identified and the work is defined. MRI works on government contract vehicles and T&M arrangements; IPSA and Agent Xero typically work on fixed-scope retainers.
The briefing itself runs 30–60 minutes. From there, timelines depend on the entity and the work: IPSA legal-AI evaluations are typically scoped over 4–8 weeks; MRI security and deployment engagements follow program timelines. The first output is a clear decision — not a discovery phase that extends indefinitely.
The briefing operates at the unclassified level and does not require sharing controlled information to frame the problem. If the work requires controlled or classified environments, MRI leads delivery with cleared personnel and private infrastructure. Specific access arrangements are confirmed at the contracting phase.
No. The first conversation is unclassified. If the program has clearance requirements, bring them to the briefing — MRI will address them in the engagement structure.
Yes. The routing model is designed to insert cleanly into existing team structures, not to displace them. MRI, IPSA, and the other entities can operate as subcontractor, teaming partner, or independent assessor depending on the contract vehicle and scope.
Next step
ASG sorts the lane, the ownership, and the next move. The right company takes it from there.
— end of brief. next steps below.
You will not get routed through layers of qualification before the real team shows up. The first response comes from people who can test fit, scope the work, and pull in whoever should own it.
One good briefing. Clear ownership after that.
No repeat briefings. No guessing who owns the next move.
How it works
Brief the problem
what has to work, what has to stay inside your boundary
Direct response
from people who can scope the work and pull in the right team
Lead team + build path
owner, deployment model, and supporting teams
Clear next move
proposal, follow-on briefing, or direct introduction